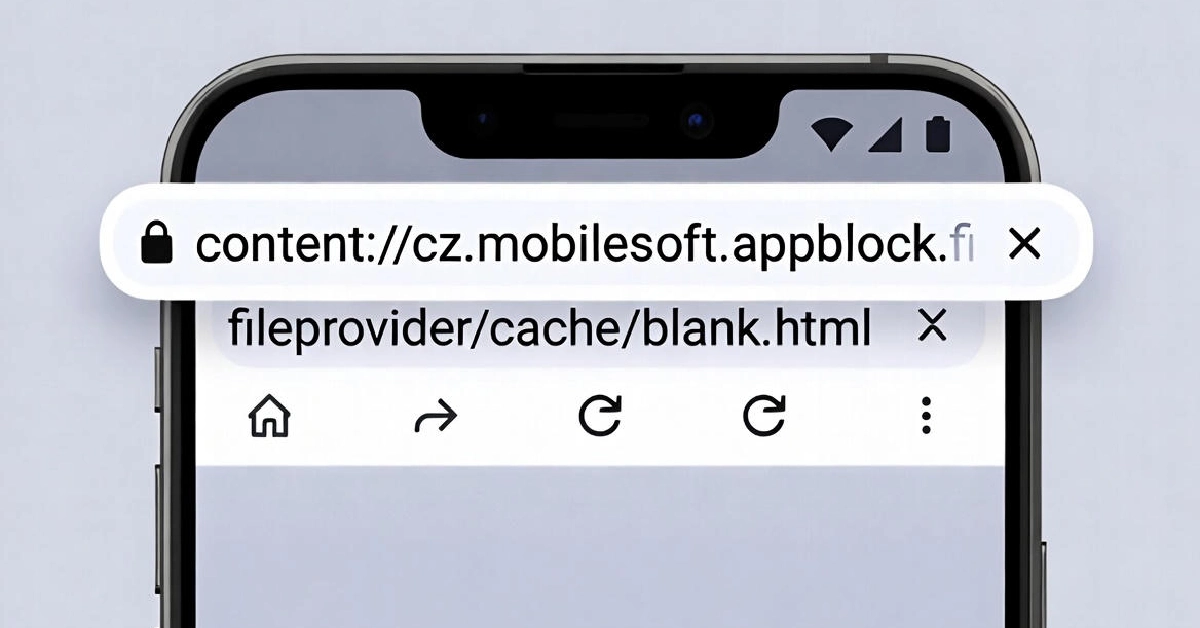
The content URI content://cz.mobilesoft.appblock.fileprovider/cache/blank.html is a secure Android file reference used by the AppBlock productivity app. It represents a cached HTML file that appears when AppBlock blocks distracting apps or websites, displaying a placeholder instead of error messages. This URI isn’t a virus or security threat—it’s part of Android’s FileProvider system that enables safe file sharing without exposing direct file paths.
What Is This URI About?
You’ve probably seen content://cz.mobilesoft.appblock.fileprovider/cache/blank.html pop up in your Android device logs or browser history and wondered if it’s something to worry about. The good news? It’s completely harmless.
This string is a Content URI tied to AppBlock, a popular app designed to block distractions and help you focus. When AppBlock restricts access to certain apps or websites, it loads this blank HTML file from its cache as a placeholder. Think of it as a polite “stop sign” rather than a jarring error screen.
Android uses Content URIs to reference files safely without revealing actual file locations on your device. This approach keeps your data private and prevents unauthorized apps from snooping around.
Breaking Down the URI Structure
Content URIs follow a specific format that makes them easy to trace back to their source.
The structure looks like this: content://<authority>/<path>/<resource>.
For content://cz.mobilesoft.appblock.fileprovider/cache/blank.html, here’s what each part means:
- content://: Identifies this as a Content URI rather than a regular file path
- cz.mobilesoft.appblock.fileprovider: The authority linking to AppBlock’s FileProvider
- cache: Points to the app’s temporary storage directory
- blank.html: The specific cached file being accessed
This structure prevents direct filesystem access and adds security layers that traditional file paths don’t offer.
Why AppBlock Uses This File
AppBlock created by MobileSoft s.r.o. helps users manage screen time and block distracting apps. The blank.html file serves multiple practical purposes within the app’s architecture.
When you try accessing a blocked app or website, AppBlock loads this cached HTML file instead of showing system errors. This creates a smoother user experience—you see a clean message explaining why access is restricted rather than confusing technical warnings.
The cached file also improves performance. Loading a small local HTML file is faster than generating blocking screens from scratch each time. This efficiency matters when you’re blocking multiple apps throughout the day.
How Android FileProvider Works
FileProvider is Android’s built-in tool for sharing files between apps securely. It replaced older methods that exposed sensitive file paths and created security vulnerabilities.
Instead of sharing actual file locations, FileProvider generates temporary Content URIs. Other apps can access these files only if they receive explicit permission. Once the permission expires or gets revoked, access disappears.
Here’s what makes FileProvider better than traditional file sharing:
- Hides real file paths from other apps
- Grants temporary access that you can control
- Works across different Android versions consistently
- Prevents unauthorized file access through sandboxing
Apps configure FileProvider in their manifest file with unique authorities. This ensures different apps don’t conflict when sharing files.
When You’ll See This URI
This URI typically appears in a few specific situations related to AppBlock’s normal operations.
You might spot it in your Android system logs when AppBlock activates blocking features. The app redirects WebViews and browsers to this cached file whenever you attempt accessing restricted content.
Browser history sometimes logs the URI when AppBlock intercepts navigation attempts. This doesn’t mean anything suspicious happened—it just shows the app doing its job.
Developers debugging apps might encounter this URI when examining file access patterns or WebView behavior. It’s a normal part of how content blocking apps interact with Android’s system.
Security and Safety Concerns
Many people worry when they see unfamiliar technical strings on their devices, but this particular URI poses no security risk.
The URI only works within AppBlock’s controlled environment. Other apps can’t access this cached file without proper permissions, thanks to Android’s sandboxing features. Even if another app tried accessing it, the system would deny the request.
FileProvider systems include built-in protections against common attacks:
- Path traversal attempts get blocked automatically
- URI permissions expire after use
- File access requires explicit permission grants
- Authority names prevent conflicts between apps
You can verify the URI’s legitimacy by checking that AppBlock is installed on your device. If you don’t have AppBlock, this URI shouldn’t appear in your logs.
Troubleshooting Common Issues
Sometimes you might run into problems related to this URI, though they’re usually easy to fix.
If AppBlock’s blocking screens don’t display properly, the cached file might be corrupted. Clearing AppBlock’s cache through your Android settings usually resolves this. Go to Settings > Apps > AppBlock > Storage > Clear Cache.
Permission errors can occur if AppBlock’s file access gets restricted. Make sure the app has necessary storage permissions in your device settings.
WebView loading failures sometimes happen when apps can’t read Content URIs properly. Updating AppBlock to the latest version often fixes these compatibility issues.
If the URI appears excessively in logs, check whether AppBlock is configured correctly. Adjust your blocking rules to prevent unnecessary redirects.
Developer Implementation Insights
Developers interested in creating similar file-sharing systems can learn from AppBlock’s approach.
Setting up FileProvider requires adding a provider declaration to AndroidManifest.xml. You’ll specify a unique authority, typically combining your package name with “.fileprovider”.
Create an XML file defining which directories your FileProvider can access. This limits exposure and improves security by restricting file sharing to specific folders.
Generate Content URIs programmatically using FileProvider.getUriForFile(). This method creates secure temporary references to files you want to share.
Grant URI permissions when sharing files with other apps using FLAG_GRANT_READ_URI_PERMISSION or FLAG_GRANT_WRITE_URI_PERMISSION. These flags control what receiving apps can do with your files.
Always validate file paths before creating URIs to prevent security vulnerabilities. Never allow user input to directly construct file paths without sanitization.
Performance and Resource Management
Properly managing cached files like blank.html improves app performance and user experience.
Cache directories store temporary data that apps can recreate if needed. Android may automatically clear cache when storage runs low, so don’t store critical data there.
AppBlock’s approach of using a small cached HTML file minimizes resource consumption. Loading this file repeatedly uses minimal memory and processes quickly.
For developers, consider implementing caching strategies based on your app’s needs. Memory caching works well for frequently accessed small files, while disk caching suits larger or persistent content.
Clean up cache resources when they’re no longer needed to prevent storage bloat. Implement lifecycle-aware cleanup that removes temporary files when activities or services shut down.
Key Takeaways
The content://cz.mobilesoft.appblock.fileprovider/cache/blank.html URI is a normal component of AppBlock’s blocking functionality. It represents Android’s secure file-sharing approach through FileProvider, which protects your privacy while enabling apps to work together.
You don’t need to worry if you see this URI in logs or browser history—it confirms AppBlock is actively managing distractions. The system is designed with security in mind and won’t allow unauthorized access to the cached file.
Understanding Content URIs helps you appreciate how modern Android apps balance functionality with security. This knowledge proves valuable whether you’re troubleshooting issues or developing your own apps.